Finray platform · The core
Corebanq
Core banking infrastructure for institutions that must prove every posting.
Atomic double-entry ledger, continuous reconciliation, payment-rail operations, and audit evidence generated from the same event stream that runs the platform.
The problem
Most regulated operators run core-banking functions on assembled stacks that cannot prove posting integrity under scrutiny. Reconciliation is retroactive. Audit evidence is retrofitted. Corebanq is built so the audit position holds without a parallel reconstruction step — every posting, every payment, every operator action recorded once on the same event stream that runs the platform.
A look at Corebanq
What Corebanq looks like in production.
Two surfaces, one platform. The end-user banking interface below — what an account holder sees when they sign in. The operator surface further down — Configurator, Ledger Browser, Reconciliation and the rest. Every action recorded here lands once on the live event stream.
Total cash position · Multi-currency · Live activity feed
End-user banking — what an account holder sees
The customer-facing side of Corebanq. A consolidated cash position, multi-currency account cards, payment workflow and FX rates, plus a live activity feed of postings and notifications — all driven by the same ledger and event stream the operator surfaces below stand on.
The customer-facing side of Corebanq. A consolidated cash position, multi-currency account cards, payment workflow and FX rates, plus a live activity feed of postings and notifications — all driven by the same ledger and event stream the operator surfaces below stand on.
Operator surface
Behind the customer experience — the operator views.
Nine views from the live Corebanq operator UI — activation, the Configurator, the Ledger Browser, ledger-account creation, continuous reconciliation, rates control, the rule editor, tariffs and velocity, and the operations control centre.
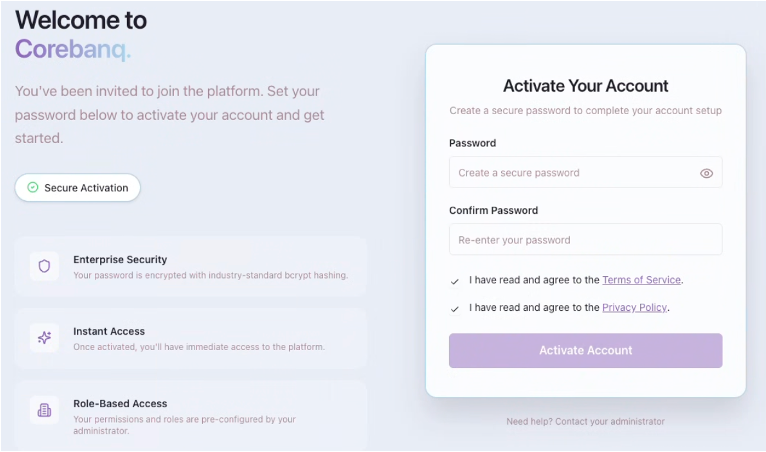
Password hashing (bcrypt) · Role-based access · Consent capture
End-user activation
End-user onboarding through the End-User Web Application. Operator-invited users set their password and acknowledge Terms of Service and Privacy Policy. Passwords are hashed using bcrypt; role and persona are pre-configured by the administrator; consent timestamps and activation metadata are recorded by the API at registration.
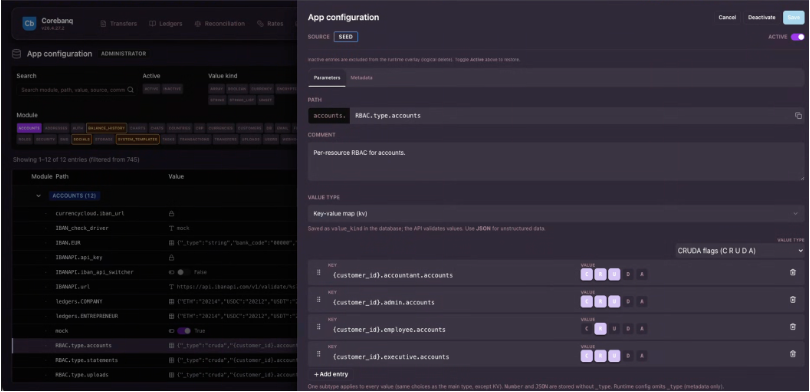
RBAC · Posting rules · Tariffs · CRUDA flags
Corebanq Configurator
Institution-specific behaviour is governed in the Corebanq Configurator — debit/credit posting rules, RBAC, tariff structures, currency catalogues, KYB onboarding flows — through versioned configuration under change-control rather than custom code releases. Granular CRUDA flags drive per-resource permissions per role. Upgrades and security patches do not require a re-merge cycle.
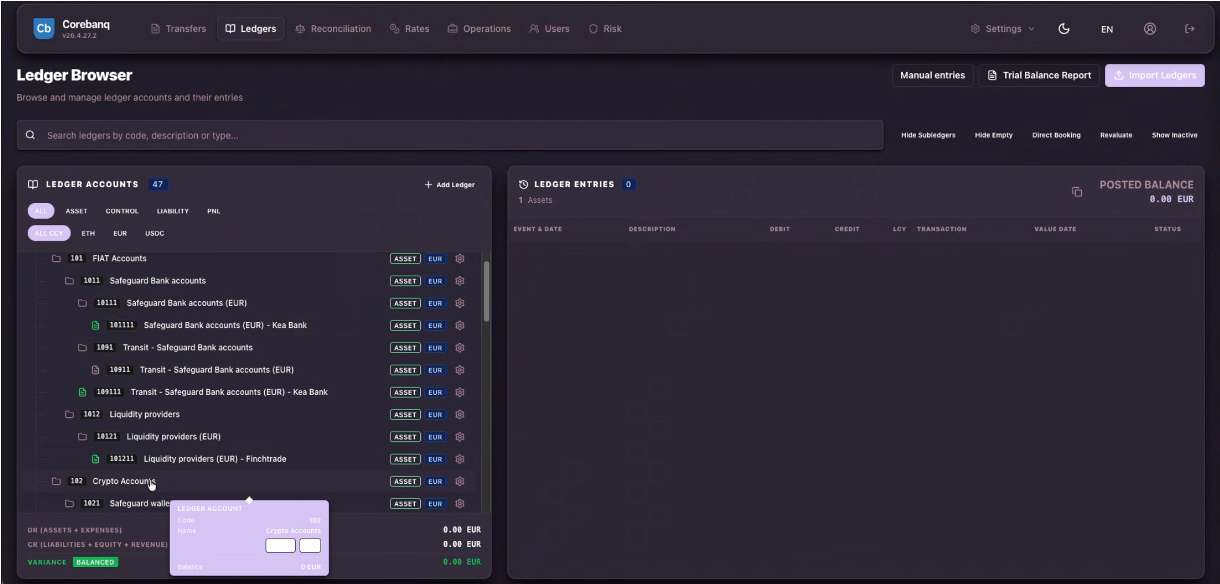
FIAT · Crypto · Transit · Liquidity · Multi-currency
Ledger Browser
The ledger, browsable. Accounts partitioned along currency, entity and ledger book at the schema level — fiat accounts, transit accounts, liquidity providers, crypto accounts. Posted balances and ledger entries are computed in real time from the same event stream that answers the auditor.
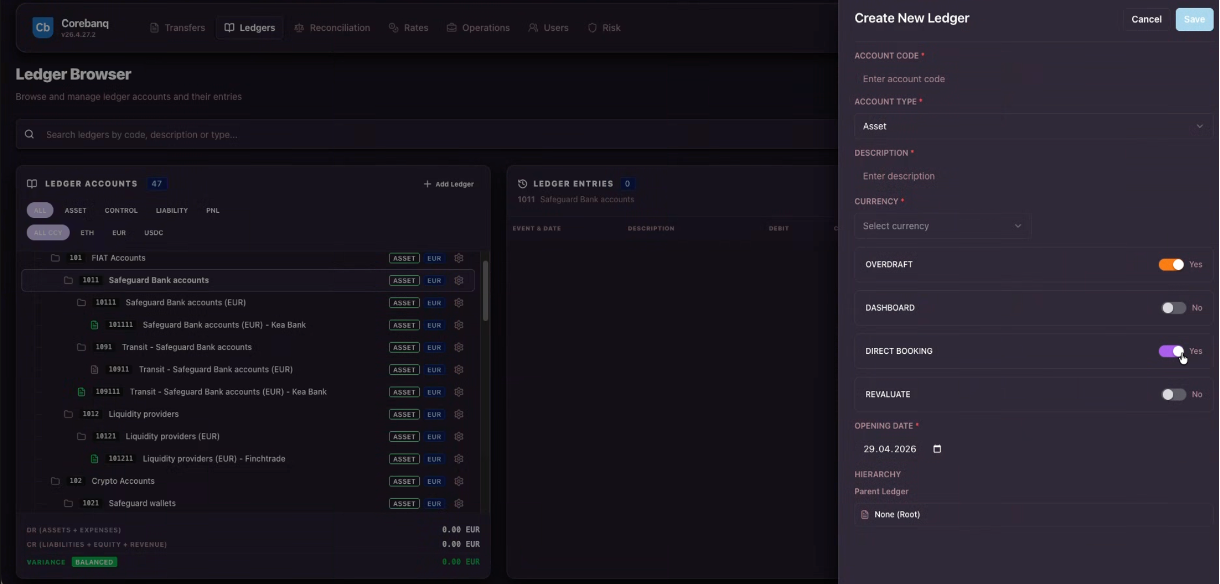
Account type · Currency · Direct booking · Revaluate
Create a ledger account
Open a new ledger account from the operations surface. Account code, type, currency, overdraft policy, direct-booking eligibility and revaluation behaviour are all set as governed configuration. The account is posting-ready under the standard configuration-change workflow rather than a custom code release.
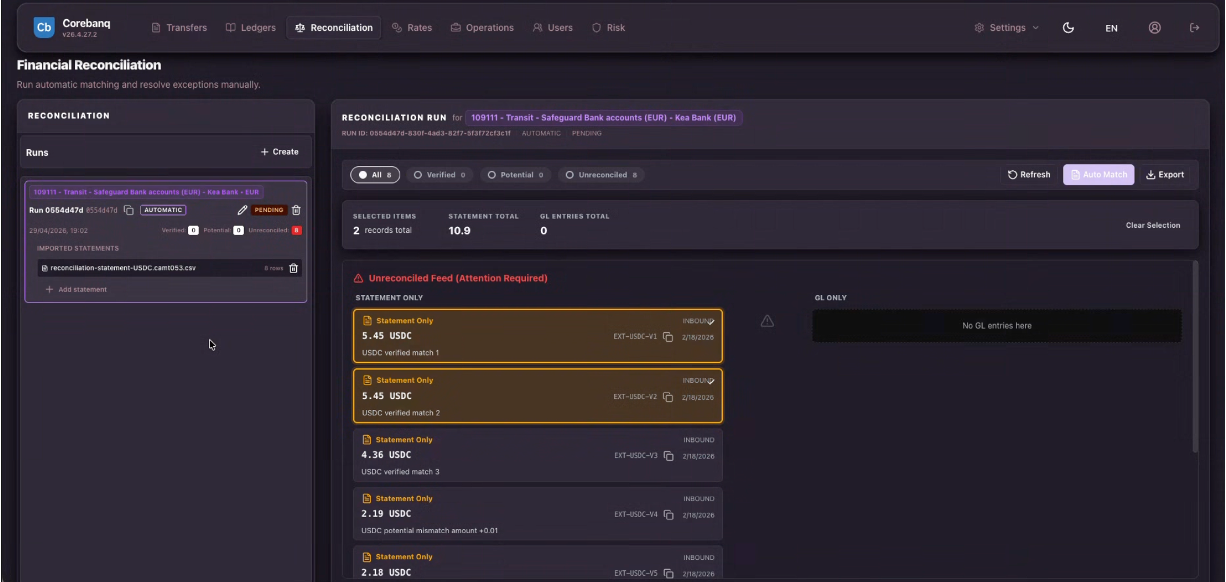
Auto match · Verified · Potential · Unreconciled
Financial Reconciliation
Continuous reconciliation against statement feeds. Verified, potential-mismatch and unreconciled items surface as operator tasks the moment they appear — auto-matched against the GL where the rules are deterministic, escalated where human judgement is required. Not an end-of-day reconstruction step.
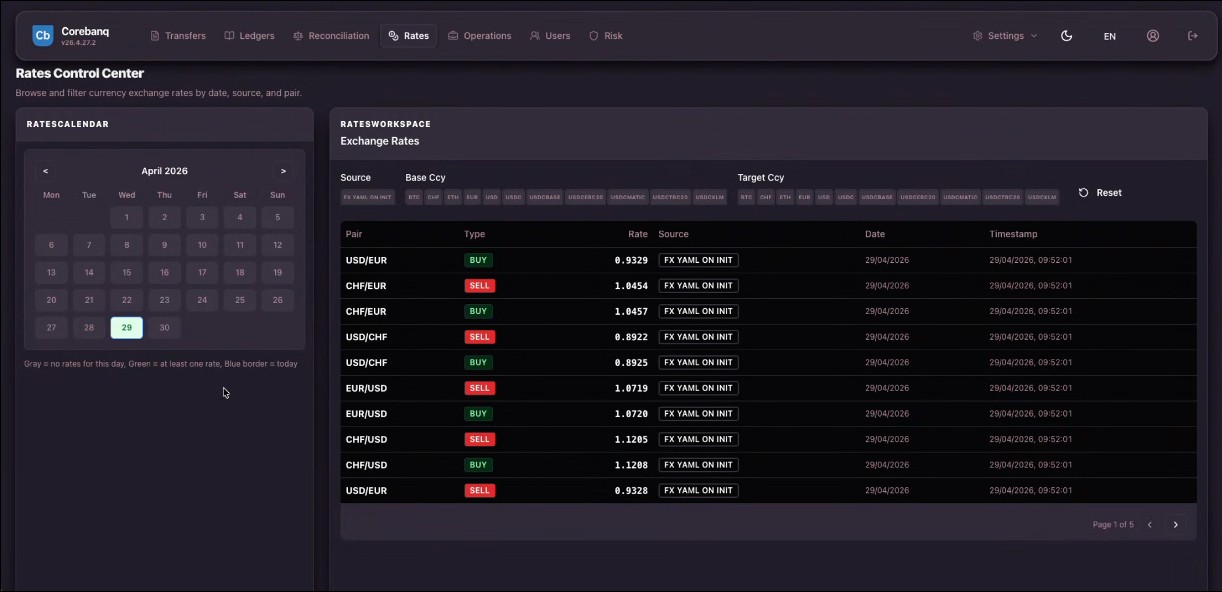
Multi-source · Per-pair buy/sell · Source attribution
Rates Control Center
Multi-source FX rate ingestion. Browse exchange rates by date, source, and currency pair — every quote carries its source provenance and timestamp. Buy/sell separation per pair, target-currency filter for the asset universe (fiat plus stable-coins). Rate history is queryable, not retroactive.
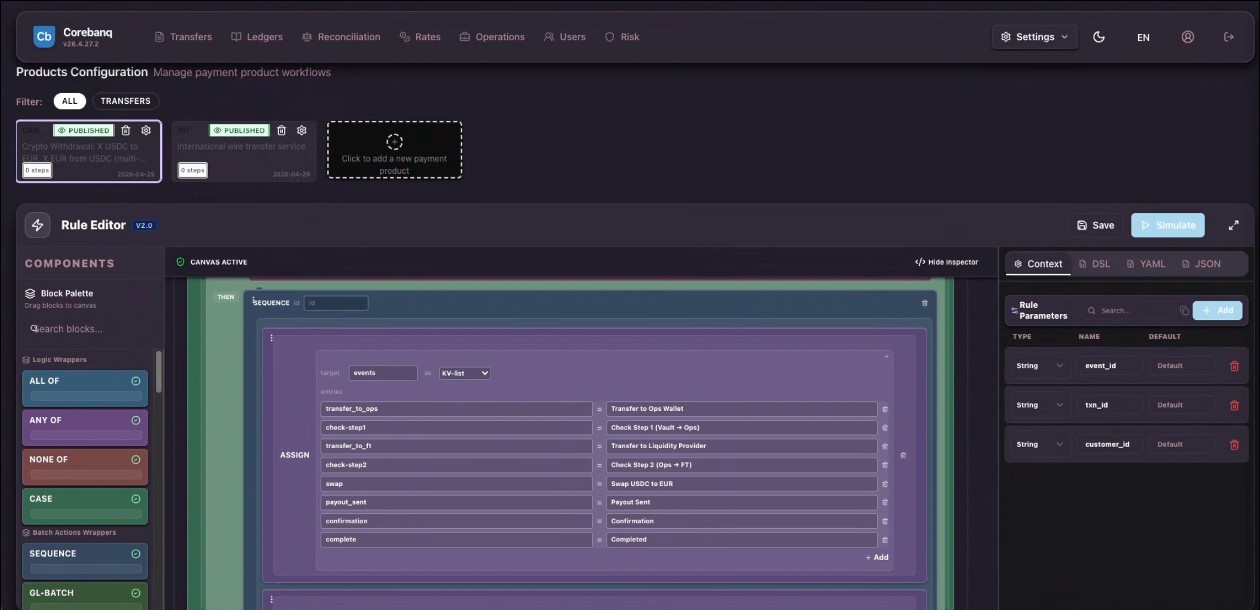
Sequence · Logic wrappers · DSL / YAML / JSON inspector
Products & Rule Editor
Visual rule editor for payment products. Compose product workflows from logic wrappers (ALL OF, ANY OF, NONE OF, CASE) and batch-action wrappers (SEQUENCE, GL-BATCH). Parameters bind to event, transaction and customer context. Inspect the same rule as DSL, YAML or JSON — the editor and the API speak the same language.
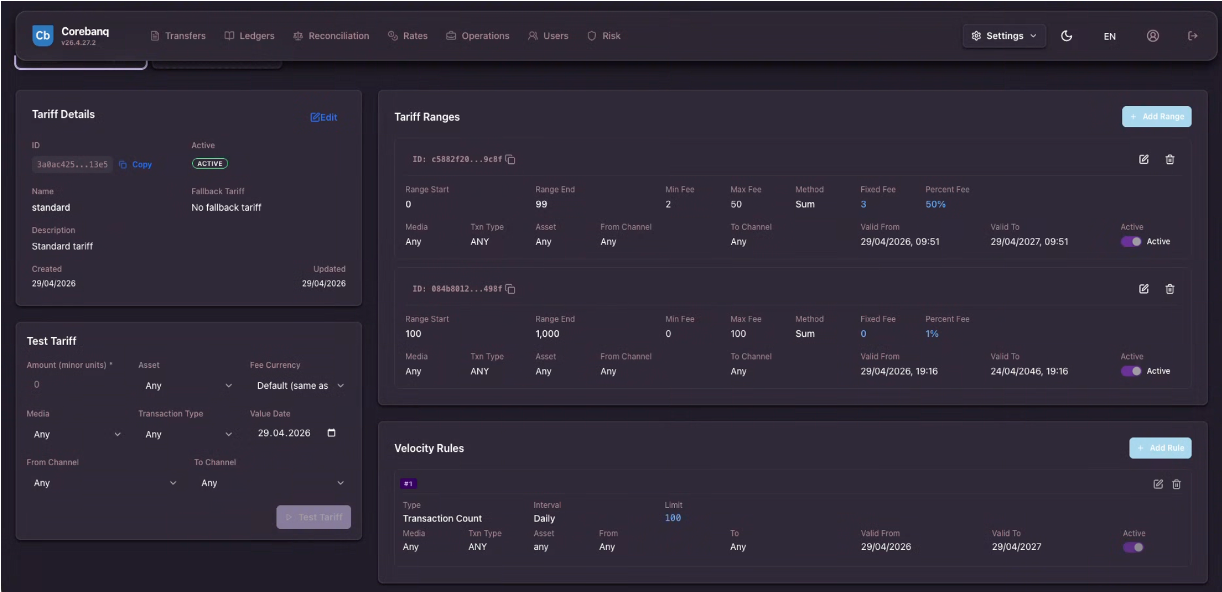
Tiered fees · Per-asset · Velocity caps · Test before activation
Tariffs & Velocity Rules
Fee schedules and operational limits as configuration. Tiered fee ranges with fixed plus percent components, per-asset and per-channel discrimination, validity windows. Velocity rules cap transaction count and notional per interval. Test the tariff against any input before activation — no production guesswork.
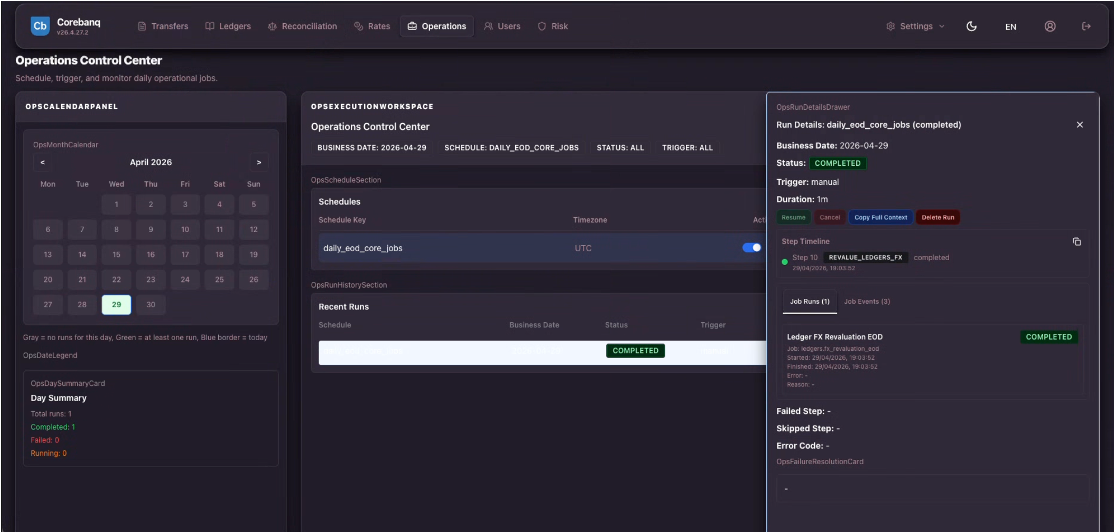
Schedules · EOD · Step timeline · Run history
Operations Control Center
Schedule, trigger and monitor daily operational jobs. EOD core-jobs run on a UTC schedule, surface a per-step timeline (REVALUE_LEDGERS_FX, etc.), and capture per-run status with full context. Pause, resume, replay — exception handling is governed through structured workflow, ownership, state history, and replayable evidence.
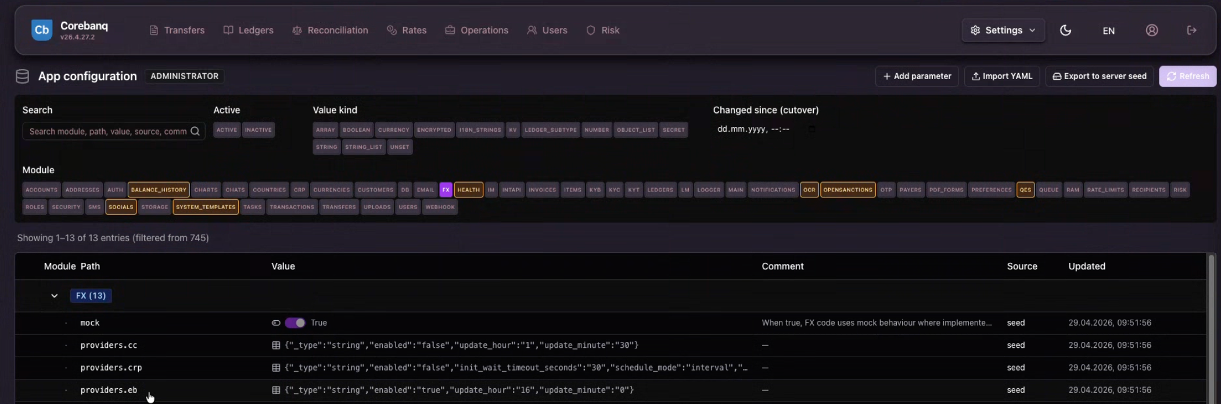
Import / Export YAML · Per-environment scope · 30+ modules
App Configuration — one governed surface
A governed configuration surface across RBAC, FX providers, OpenSanctions, QES, system templates, payment providers, KYB, tariffs, and operational modules — every parameter under change-control and versioned per environment. Import / export YAML, scope per environment, filter by module / value-kind / source. The current scope spans roughly 745 parameters; new modules ship with their parameters under the same control regime.
A governed configuration surface across RBAC, FX providers, OpenSanctions, QES, system templates, payment providers, KYB, tariffs, and operational modules — every parameter under change-control and versioned per environment. Import / export YAML, scope per environment, filter by module / value-kind / source. The current scope spans roughly 745 parameters; new modules ship with their parameters under the same control regime.
Representative UI capture · synthetic values · not a live customer environment
What Corebanq does
Capabilities
-
Atomic double-entry ledger
Posting integrity enforced at write time with Dr/Cr parity. The ledger rejects unbalanced postings at write time. Reconciliation then addresses external-feed, counterparty, and operational mismatches as explicit tasks.
-
Multi-asset accounts model
Multi-currency, multi-entity, multi-ledger partitioning at the schema level — not as tags on a flat balance.
-
Payment operations
SIC, SEPA, SWIFT and instant rails — with exception workflow as a structured object, not an email chain.
-
Continuous reconciliation
Differences surface as operator tasks the moment they appear — not a quarterly PDF report at end-of-day.
-
ISO 20022 translator
Standardised messaging for pacs / pain / camt schemas, with idempotency rules and replay-safe ingress.
-
Compliance & RBAC
Real-time KYT/AML hooks, role-based access control, identity / persona filtering — every action carries the actor and the policy version.
-
Immutable event stream
The same record drives operations and answers the auditor. No separately generated audit-trail report.
Engineered for SIC Instant
Instant rails are not bolted on.
SIC Instant Payments — operated by SIX Group on SNB mandate — imposes scheme-rule constraints that a batch-era ledger cannot meet under load. Corebanq, paired with the Zahlex payment-operations module, is built around those constraints from the first commit.
Zahlex appears in the SIX Interbank Clearing service-provider context for Swiss payment infrastructure. Connect a FINMA-supervised institution's SIC IP gateway to Zahlex; message validation, reconciliation, exception flow, and reversal handling are designed-in, not assembled. Connectivity remains within the licensed institution's regulatory perimeter.
Finray is not a bank, payment institution, or e-money institution. Corebanq and Zahlex operate within the licensed institution's regulatory perimeter; the institution remains responsible for regulated activity.
- Message format ISO 20022 (pacs.008 / pacs.002 / camt.054)
- Availability 24 / 7 / 365 — no settlement window
- Latency target Sub-10-second end-to-end
- Reconciliation Continuous tolerance check, not end-of-day
- Reversal handling Structured per scheme rulebook — every transition recorded
- Service-provider context Zahlex appears in the SIX Interbank Clearing context for SIC infrastructure
- FINMA scope Operates within the licensed institution's perimeter
Why it is different
A modern, configured, independently-tested core-banking platform.
-
Modular and composable
Corebanq is modular core-banking infrastructure. Adopt the modules an institution actually needs — ledger, accounts, payments, FX, tariffs, RBAC — and assemble them through versioned API contracts under change-control. Not a monolithic licence.
-
Configured, not customised
Institution-specific behaviour is governed through versioned configuration under change-control — debit/credit posting rules, ledger entries, transaction lifecycles, tariff structures, currency catalogues — without forking the application codebase.
-
Modern stack, modern primitives
Built on modern infrastructure — Kubernetes + ArgoCD + ECR with security scanning gates, AWS-managed services, AES-256 at rest, TLS 1.3 in transit, SOPS + AWS KMS for secrets. Not a 20-year-old core re-clad as cloud-native.
-
Independently penetration-tested
Penetration-tested by independent Swiss and EU security firms under NDA. The most recent independent test was completed in April 2026 and covered the web and API surface, the AWS account, and the Kubernetes infrastructure. The security firm's identity, the test report, and remediation evidence for material findings are available under NDA as part of vendor due diligence.
Deployment
Three deployment models, one operating model.
Pick the deployment that matches the institution's IT footprint and data-residency posture. The platform behaviour is identical across all three; only the operating boundary changes.
-
Cloud SaaS
Multi-tenant cloud, fully managed
Multi-tenant deployment on Finray-managed infrastructure. Suitable for EMIs, PIs, and smaller FinTechs that want rapid go-live with minimal IT overhead.
-
Private SaaS
Single-tenant cloud, dedicated
Single-tenant cloud deployment with dedicated infrastructure. Designed for neobanks, larger EMIs/PIs, and regulated institutions that require enhanced data isolation.
-
Enterprise License
On-premise or private cloud
On-premise or private-cloud deployment with perpetual license. Optimal for large banks and institutions that require maximum control over infrastructure and data residency.
Topology in the regulatory frame
Single-tenant customer-cloud is more controllable, not easier.
Regulators do not grant a safe harbour for any deployment model — neither multi-tenant SaaS nor single-tenant in a customer cloud account. DORA (accessed 2026-05-08), the EBA Outsourcing Guidelines (accessed 2026-05-08), PRA SS2/21 (accessed 2026-05-08), FCA SYSC 8 (accessed 2026-05-08) and FINMA Circular 2018/3 (accessed 2026-05-08) all begin from the same load-bearing point: the financial entity remains fully accountable for the service, even where technology operation is outsourced. What these regimes require, and what supervisors examine, is provable control: audit and access rights, a credible exit strategy, subcontractor visibility along the chain, concentration-risk management and operational-resilience evidence.
For a Tier-2 bank, an authorised EMI/PI, or a FINMA/FCA/PRA-supervised firm running core banking as a critical function, single-tenant deployment in the institution’s own AWS, Azure or GCP cloud account is structurally better aligned with these obligations than multi-tenant SaaS in a vendor-controlled cloud — provided the institution can operate cloud controls at regulated-firm maturity. The structural alignment is not about software quality. It is about which side of the boundary holds the control evidence the supervisor will ask to see.
First, accountability sits with the regulated firm by law, and a single-tenant deployment makes that accountability operational. The institution holds direct access to infrastructure logs, identity-and-access-management state, network controls, backup evidence and configuration history — the artefacts that constitute an audit pack rather than abstractions about the vendor’s posture. Second, FINMA Circular 2018/3 requires that the company, its audit firm and FINMA can inspect the outsourced function and that outsourcing must not make FINMA supervision more difficult. In multi-tenant SaaS the audit often runs through pooled audit reports, shared-environment constraints and contractually mediated production access; in single-tenant customer-cloud the audit pack is account-level evidence the institution can produce on demand. Third, the EBA requires a documented exit strategy for critical or important functions covering business impact analysis, resources, roles and time-to-cutover. In single-tenant deployments, data and infrastructural artefacts already sit inside the institution’s perimeter, so exit can be designed earlier and tested more rigorously than where the runtime depends on a vendor’s export tooling.
Fourth, the subcontractor chain does not disappear — it becomes navigable. Both deployment patterns produce a chain that includes the cloud provider, observability, security tooling and managed-service inputs. In single-tenant customer-cloud, the institution holds the hyperscaler relationship directly and can separate software-vendor risk from cloud-infrastructure risk in its register of information. Fifth, concentration risk has moved to the centre of supervisory attention. DORA Article 29 requires assessment of dependency on non-substitutable ICT providers and multiple arrangements with the same or connected providers. Single-tenant customer-cloud does not eliminate this concentration — Amazon Web Services EMEA, Google Cloud EMEA, Microsoft Ireland Operations and Oracle Nederland are on the first ESAs Critical Third-Party Provider designation list of November 2025 (accessed 2026-05-08) — but it does reduce the additional layer of concentration that accumulates at the core-banking SaaS vendor.
The maturity precondition matters. An institution without operational SIEM/SOC, IAM discipline, backup testing, change control, incident-response runbooks, encryption and key-management governance and platform engineering capability does not benefit from single-tenant; it inherits expense and responsibility without the control return. Multi-tenant SaaS is the right choice for less-critical functions, fast launches, smaller EMIs/PIs, and institutions building toward platform maturity. The FCA states there is no fundamental reason public cloud services cannot be used in a compliant manner where institutions properly consider the controls (FCA FG16/5, accessed 2026-05-08).
The UK direction of travel is toward more, not less, third-party transparency. The PRA, FCA and Bank of England operational-incident-and-third-party-reporting regime takes effect on 18 March 2027 and broadens reporting from material outsourcing to wider material third-party arrangements covering banks, designated investment firms, authorised EMIs and authorised PIs. The model that wins under that regime is the one where the institution can present a navigable dependency map rather than a vendor-supplied assurance pack.
Multi-tenant SaaS sells speed and simplicity. Single-tenant customer-cloud sells provability of control. For regulated core banking in 2026, provability is the load-bearing artefact. Single-tenant in customer-cloud is not “easier” — it is more controllable. That distinction is the buyer-DD signal that holds up under examination.
Full primary-source analysis
The eight control axes — outsourcing classification, CTPP designation, audit rights, sub-contractor chain, exit strategy, data sovereignty, concentration risk and operational resilience — are encoded as a primary-source-cited buyer guide on Finray Intelligence. Corebanq is recused from any qualitative ranking on the buyer guide; the analysis is about the topology category, not Corebanq specifically.
Read “Core banking deployment topology and regulatory alignment”Applied on Corebanq
Solutions built on Corebanq
-
SwissKonto
Swiss corporate banking experience built on Corebanq.
-
Zahlex
Payment operations with validation, enrichment, and exception handling. Appears in the SIX Interbank Clearing service-provider context for Swiss SIC infrastructure.
-
BitKonto
Digital-asset treasury operations for custody-adjacent accounts, with Fireblocks-backed key management.
Who Corebanq is built for
Regulated institutions whose audit position cannot drift.
-
Switzerland
FINMA-supervised banks + Art. 1b FinTech firms
FINMA Banking Ordinance · FINMA Circulars · FinIA / FinSA · SNB SIC oversight
-
EU / EEA
Payment + e-money institutions
PSD2 · EBA Guidelines · SEPA Rulebook · MiCA-adjacent CASPs
-
United Kingdom
FCA-authorised PI / EMI firms
FCA SUP 16 · PSR · COREP / FINREP reporting · FCA Operational Resilience
-
Canada
RPAA-regulated PSPs + FINTRAC-registered MSBs/FMSBs
Retail Payment Activities Act · PCMLTFA · FINTRAC reporting
Plumery (Amsterdam) is an authorized integration partner for Corebanq. Plumery provides the headless, API-first customer-experience layer — web and mobile banking applications, pre-built journeys, MACH-architecture cloud services — on top of the Corebanq account and payment APIs.
- Customer-facing layer. Headless, API-first banking screens — web and mobile — on top of Corebanq's account and payment APIs.
- Composable architecture. Modular, API-first, cloud-native, headless (MACH) stack that talks to Corebanq through versioned contracts.
- Faster time to market. Pre-integrated UI components and ready-made digital banking journeys reduce frontend build effort.
Finray Technologies and Plumery B.V. are independent contractors. Neither party is an agent of the other and is not authorized to make any representation, contract, or commitment on behalf of the other party.
Other integrations
-
Plumery
Customer-facing experience layer (headless, API-first)
-
Fireblocks
Custody and key management for digital-asset operations
-
TRM Labs
Blockchain analytics — via the XZiel compliance toolchain
-
OpenSanctions
Sanctions and PEP screening dataset (BYOL-eligible)
-
SIX Group
SIC Interbank Clearing service-provider context
-
AWS
Managed cloud — KMS, EKS, ECR, ArgoCD, SOPS-encrypted secrets
API access
Book a briefing to get the full API reference.
docs.corebanq.com hosts the introduction and the design overview. The production API reference — endpoint catalogue, message schemas, idempotency rules, rate limits, integration playbook — is issued under briefing scope, alongside test-environment access and a direct line to Finray engineering.
- Endpoint catalogue + JSON schemas
- Idempotency + retry rules
- Rate-limit envelopes + back-pressure semantics
- Webhook payload reference
- Test-environment access + sandbox keys
- Direct contact with Finray engineering
Editorial — Finray Intelligence
Vendor-neutral buyer guides for the categories Corebanq competes in.
Finray Intelligence publishes evidence-disciplined buyer guides for the regulated-software categories Corebanq ships in, plus forensic registers of every successfully authorised EMI/PI in the EEA + UK. Where Corebanq appears in those guides it is recused from any qualitative ranking; every claim is sourced to a regulator page, vendor page or official journal with an accessed-date. See the editorial methodology for the full principles.
-
Buyer guide
FCA Supplementary Safeguarding Regime (PS25/12)
Architectural radar for FCA PS25/12 covering CASS 15 (operational), CASS 10A (resolution pack), SUP 3A (annual safeguarding audit) and SUP 16.14A (REP027 monthly return), in force from 2026-05-07. 18 atomic controls with rule-level FCA Handbook anchors. 10 named UK forensic cases (Premier FX, Allied Wallet, Wirecard CS, Rational FX, Xpress Money, Monneo, JNFX, Biilz, Currency Matters) plus the Ipagoo court cross-reference. Corebanq recused from ranking.
Read methodology -
Buyer guide
Safeguarding reconciliation as solvency discipline
Architectural radar for EMI and PI safeguarding under PSD2 Article 10, EMD2 Article 7, FCA PS25/12 (CASS 10A, CASS 15, SUP 3A, SUP 16) and forward-looking PSD3/PSR. 15 control nodes (account designation, segregation, daily reconciliation, intraday integrity, D+1 comparison, books-and-records-at-any-time-no-delay, monthly safeguarding return, resolution pack, annual safeguarding audit, governance 1st/2nd line separation, third-party oversight, settlement-account-not-itself-safeguarding, concentration risk, group oversight). 4 named enforcement cases (BlueSnap, Foxpay, Biilz, Currency Matters); 6 vendors mapped to controls. Corebanq recused from ranking.
Read methodology -
Buyer guide
Core banking deployment topology and regulatory alignment
Primary-source-cited buyer guide comparing multi-tenant vendor-controlled SaaS and single-tenant customer-cloud deployment topologies for core banking software under DORA, EBA outsourcing, PRA SS2/21, FCA SYSC 8, FINMA Circular 2018/3, GDPR, EU Cybersecurity Act and the FSB third-party-risk toolkit. Eight control axes encoded with primary-source citations and accessed-dates. Corebanq recused from ranking.
Read methodology -
Buyer guide
EU/UK PI/EMI core banking selection
Decision graph for EU/UK Payment Institutions and E-Money Institutions selecting core banking software under PSD2/PSD3/PSR, DORA and AML obligations. 14 vendors (Mambu, Tuum, Thought Machine, Temenos, Finastra, 10x, SaaScada, Engine, Pismo, Vodeno and others) mapped to the regulatory anchors. Corebanq recused from ranking.
Read methodology -
Forensic register
EMI / PI licensing-success forensic register (EEA + UK)
571 successful EMI/PI/AISP-only authorisations across the FCA, DNB, Bank of Lithuania and HNB registers. Every entity named, jurisdiction and institution class encoded; PSD2 Annex I + EMD2 service-scope as node breadth. Verified-floor benchmark for EMI/PI authorisation outcomes.
Open the register
FAQ
Frequently asked questions.
-
What is Corebanq?
Corebanq is the core-banking platform for regulated financial institutions — an atomic double-entry ledger, multi-currency and multi-entity accounts model, and SIC, SEPA, SWIFT and instant payment rails with continuous reconciliation and an immutable event stream as the audit record. Real-time analytics, an ISO 20022 translator, and KYT/AML hooks ship as part of the same operational surface.
-
Which payment rails does Corebanq support?
SIC (Swiss real-time gross settlement under SNB oversight), SEPA Credit Transfer and SEPA Instant, SWIFT cross-border, and instant payment schemes. Exception workflow is built in — each exception is a structured object with state, owner, and history.
-
Is Corebanq engineered for SIC Instant Payments?
Yes. The Zahlex payment-operations module — built on Corebanq — implements the SIC Instant scheme constraints by construction: ISO 20022 message format, 24/7/365 availability, sub-10-second end-to-end target, strict reconciliation tolerances, and structured reversal handling. Zahlex appears in the SIX Interbank Clearing service-provider context for Swiss payment infrastructure. Corebanq + Zahlex give a FINMA-supervised institution a route to SIC IP connectivity that does not require bolting an instant-payment workflow onto a batch-era ledger. Connectivity remains within the licensed institution's regulatory perimeter — Finray is not a bank, payment institution, or e-money institution.
-
How does Corebanq enforce posting integrity?
Posting integrity is enforced at write time, not at reconciliation time. The ledger rejects unbalanced postings by construction, and the event stream that drives operations is the same record auditors read — there is no separately generated audit-trail report.
-
How is reconciliation handled?
Reconciliation runs continuously, not at end-of-day. Discrepancies surface as tasks the operator can act on — not as quarterly PDF reports. There is no end-of-day reconstruction step.
-
How does the accounts model handle multi-currency and multi-entity?
Corebanq's accounts model is partitioned along three axes — currency, entity, and ledger book — at the schema level, not as a tag on a flat balance. A multi-currency, multi-entity institution can run consolidated reporting and per-entity isolation off the same primitive without mirror-account workarounds.
-
What is the Corebanq Configurator?
The Corebanq Configurator is where institution-specific behaviour is set — debit/credit posting rules, ledger entries, transaction lifecycles, tariff structures, currency catalogues, KYB onboarding flows. Customisation lands in configuration, not in a forked codebase, so upgrades and security patches do not require a re-merge cycle.
-
How has Corebanq been security-tested?
Corebanq has been independently penetration-tested by Swiss and EU security firms under NDA. The most recent independent test was completed in April 2026 and covered the web and API surface, the AWS account, the Kubernetes infrastructure, plus over-the-shoulder review of Fireblocks and Cloudflare Zero Trust posture. The security firm's identity, the test report, and remediation evidence for material findings are available under NDA as part of vendor due diligence.
-
What does the integration surface look like?
Corebanq exposes a typed JSON-over-HTTPS API for postings, accounts, payments, and the event stream — plus webhook subscriptions for downstream consumers. Authentication, rate limiting, and tenant isolation are handled at the API gateway. The introduction and design overview are public at docs.corebanq.com. The full API reference (endpoint catalogue, message schemas, idempotency rules, rate limits, integration playbook) is issued under briefing scope alongside test-environment access and direct contact with engineering.
-
How is Corebanq deployed?
Three licensing models are supported: Cloud SaaS (multi-tenant managed deployment for EMIs, PIs, and smaller FinTechs that want minimal IT overhead); Private SaaS (single-tenant cloud with dedicated infrastructure for neobanks, larger EMIs/PIs, and institutions that need enhanced data isolation); and Enterprise License (on-premise or private-cloud deployment with perpetual license for large banks and institutions that need maximum control over infrastructure and data residency). Customer-managed-key options are available on request.
-
How does the Plumery integration work?
Plumery (Amsterdam) is an authorized integration partner for Corebanq. Plumery provides the customer-facing banking experience layer — headless, API-first, web and mobile — on top of Corebanq's account and payment APIs. Institutions that want a modern customer journey paired with Corebanq's ledger can take Plumery's pre-built screens and journeys and connect them to Corebanq through versioned API contracts. Finray Technologies and Plumery B.V. operate as independent contractors under the Finray Partner Agreement.
-
Who is Corebanq built for?
Swiss FINMA-licensed institutions and Art. 1b FinTech firms, EU/EEA payment and e-money institutions, UK PI/EMI firms regulated by the FCA, and Canadian RPAA-regulated PSPs and FINTRAC-registered MSBs/FMSBs. The applied solutions SwissKonto, Zahlex, and BitKonto are built on Corebanq.
-
Is Finray a bank?
No. Finray is a software company, not a bank, payment institution, or e-money institution. Corebanq operates within the customer's regulatory perimeter — the licensed institution remains responsible for regulated activity.
On Gartner Peer Insights
Corebanq is listed on Gartner Peer Insights. Read reviews from verified end users — or add your own.
Read Corebanq reviews on Gartner Peer InsightsThe GARTNER PEER INSIGHTS logo is a trademark and service mark of Gartner, Inc. and/or its affiliates, and is used herein with permission. All rights reserved. Gartner Peer Insights reviews constitute the subjective opinions of individual end users based on their own experiences and do not represent the views of Gartner or its affiliates.
Book a briefing
Book a briefing.
Bring one operating problem. We will map it to ledger state, risk decisions, control evidence, and deployment constraints.